Most organizations treat DNS as plumbing. It runs constantly in the background, moving enormous volumes of traffic, and almost nobody looks at it closely. That assumption has a cost.
DNS is not just a name resolution service. At the metadata level, it is a continuous behavioral record of everything happening on a network — which hosts are talking to what, how often, with what outcomes, and through what infrastructure. The security teams that have started treating it that way are finding things that nothing else in their stack was catching.
NetQuest NetworkLens™ captures that record at carrier scale — unsampled, continuous, and structured for AI-driven analysis. Here is what it reveals.
The Protocol Everyone Trusts and Nobody Watches
There is a reason DNS has become one of the most consistently exploited protocols in modern attack campaigns: it is almost universally permitted across network boundaries, generates enormous volumes of traffic that provide deep cover for low-and-slow activity, and has historically received almost no behavioral scrutiny at scale.
The problem isn’t that organizations lack DNS logs. Most have them. The problem is that a log of individual queries tells you almost nothing about what is actually happening. The behavioral signals that matter — resolution patterns over time, response characteristics, the relationship between queries and outcomes across a subscriber population — only emerge when you can see the full picture continuously, without sampling gaps.
In carrier and government networks, where DNS traffic runs into the billions of transactions per day, that kind of visibility has historically been out of reach. NetworkLens was built specifically to change that.
The Threats Living Inside DNS Traffic Right Now
Six distinct threat categories live inside DNS metadata, and most organizations have no visibility into any of them. What they all share is that none of them are detectable through conventional security tooling, but all of them are are visibile with continuous DNS metadata at scale.
Data Leaving the Network Through the Resolver
DNS was never meant to carry data payloads. But the same flexibility that makes it useful — multiple record types, generous payload capacity, near-universal network permissions — also makes it a capable exfiltration channel for anyone patient enough to use it.
Tools purpose-built for this technique encode data inside DNS queries and responses, constructing a covert channel that bypasses data loss prevention controls, traverses firewalls, and operates entirely within traffic that most security platforms treat as benign. At low volume, spread across a busy subscriber base, there is nothing in a conventional security stack that will catch it.
The detection surface exists entirely at the metadata layer. The behavioral signatures are there — in the characteristics of the queries being generated, in the structure of the responses coming back, in the patterns that accumulate over time across a continuous, unsampled stream. Without that stream, the channel stays open indefinitely.
Nation-state operators have sustained DNS-based covert channels inside carrier and government networks for months without detection. The traffic looked legitimate because the protocol was legitimate. The behavior was not.
Malware That Announces Itself
A category of malware generates large numbers of domain lookup failures as a side effect of how it operates. It cycles through algorithmically generated names looking for its command-and-control server. Most of those names don’t exist. The result is a characteristic burst of failed resolutions that, at sufficient volume, is one of the clearest behavioral signals in network security.
The catch is that this signal is only visible in aggregate. A single failed resolution means nothing. Hundreds of them, from the same host, for domains that share no lexical relationship to anything in legitimate use, is a different story entirely.
NetworkLens builds that picture continuously. The DNS dataset captures resolution outcomes and transaction characteristics across every session, giving analysts the behavioral baseline that makes this kind of activity unmistakable — even when individual events are low-volume and spread across time.
Malware That Announces Itself
Network reconnaissance doesn’t require special tools or elevated privileges. It requires DNS queries and patience.
An attacker with an initial foothold can use DNS to systematically build a map of an organization’s internal infrastructure — naming conventions, server roles, mail architecture, authentication services, trust relationships — without ever touching a vulnerability scanner or triggering an IDS signature. The queries look like ordinary resolution activity. The pattern, observed over time and across query types, tells a completely different story.
This technique has been documented as a precursor step in multiple significant intrusions against government and defense targets. The window to detect it is before the reconnaissance is complete and the attacker knows where to go next. DNS metadata at scale is the earliest available detection surface.
Detecting DNS reconnaissance requires population-level visibility across query types and volumes over time — not just a log of individual lookups. By the time a signature fires, the map is already drawn
Command-and-Control Infrastructure Built to Survive Takedowns
IP blocklists work until they don’t. Sophisticated threat operators have long since adapted their infrastructure to rotate faster than blocklist updates can follow; cycling through address space at intervals short enough that a blocked IP is irrelevant within minutes.
The mechanism that makes this possible leaves a distinctive trace in DNS metadata. Keeping IP addresses cycling that rapidly requires unusually aggressive caching behavior, TTL values so low that the normal logic of DNS resolution breaks down. A domain whose resolved addresses change on nearly every query, with TTL values that effectively disable caching, stands out sharply against the baseline behavior of legitimate infrastructure.
This is a detection that exists entirely in DNS metadata. It is not visible in endpoint logs. It does not appear in firewall rules. It requires the continuous, transaction-level record that NetworkLens provides across 100% of traffic, without exception.
C2 Traffic Hiding Behind Infrastructure You Already Trust
Some threat techniques don’t try to evade detection — they render detection irrelevant by operating through infrastructure that security teams have explicitly decided to trust.
Content delivery networks and major cloud platforms are everywhere in legitimate traffic. Threat operators have found ways to route command-and-control communications through shared CDN infrastructure, making the traffic appear to originate from — and terminate at — trusted providers. Network defenders see connections to familiar, high-reputation infrastructure. The actual communication path is invisible to any tool that relies on IP reputation.
The tell is in the DNS resolution chain. A newly-registered domain with no history, no web presence, and no plausible legitimate purpose that delegates through a major CDN to unknown infrastructure is not behaving like a legitimate domain. NetworkLens captures the full resolution chain at carrier scale, surfacing these relationships across the subscriber population before the C2 channel is established.
Your Own Infrastructure Weaponized Against Others
DNS amplification attacks don’t just target organizations — they recruit their infrastructure. Misconfigured resolvers across carrier networks can be enlisted as unwitting amplifiers, generating traffic volumes far exceeding what the attacker directly controls.
For carriers managing millions of customer premises devices, this is less a hypothetical than an ongoing operational reality. The enumeration and staging activity that precedes these attacks is visible in DNS metadata: anomalous query type patterns, unusual flag behavior, high-rate queries to specific authoritative zones. All of this can be spotted before any attack traffic is generated.
Carrier-scale unsampled DNS metadata is the only practical mechanism to identify open resolver exposure across a full subscriber base. Sampled flow data misses the low-volume probing. Application-layer controls don’t reach embedded CPE devices. The visibility lives at the wire.
What NetworkLens™ Sees That Nothing Else Does
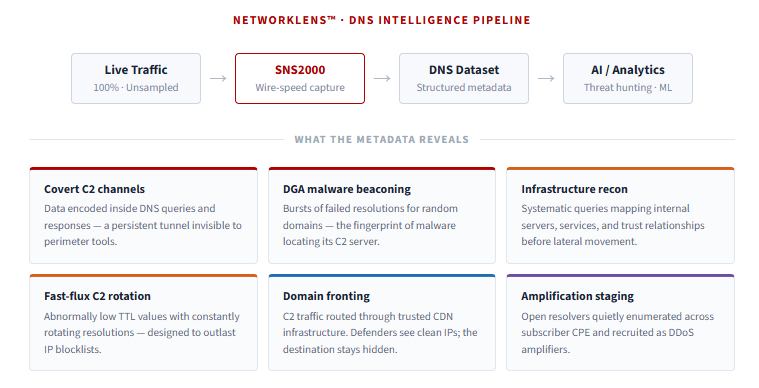
The SNS2000 captures DNS intelligence at wire speed across carrier-grade infrastructure — every transaction, every outcome, every resolution chain, structured and delivered continuously via IPFIX and Kafka for direct integration into analytics and AI pipelines.
The scenarios above share a common thread: none of them are visible in individual events. They are behavioral patterns that accumulate over time, across a population, in data that has to be present before the analysis can happen. Sampled flow data cannot produce them. After-the-fact log review finds them too late. Full packet capture at this scale is operationally impractical.
DNS has been a persistent blind spot for network security operations because the metadata required to hunt in it at scale simply wasn’t available. That’s the gap NetworkLens was built to close.
If your security operations team isn’t treating DNS as a first-class intelligence source today, we’d welcome a conversation about what that change looks like and what it makes possible.
